Acronis True Image 2020 Build 22510 + Patch
App info
Complete cyber protection comes from features that simultaneously address the safety, accessibility, privacy, authenticity, and safety of your data
Safety
Ensure that a reliable copy of your data is always available
Dual Protection
Replicate your local backup in the cloud* automatically so you always have an off-site copy available for recovery. Automates your 3-2-1 backup strategy, completing the backup and replication simultaneously. Learn more
Full Image Backup
Protect everything to recover anything. Having a mirror image of your system disk or a selected partition means you can easily recover whatever you need – from your full system to an individual file or folder.
File and Folder Backups
Control the nature of your backups. Select individual files and folders that you want specific replicas of when you don’t want a full image copy.
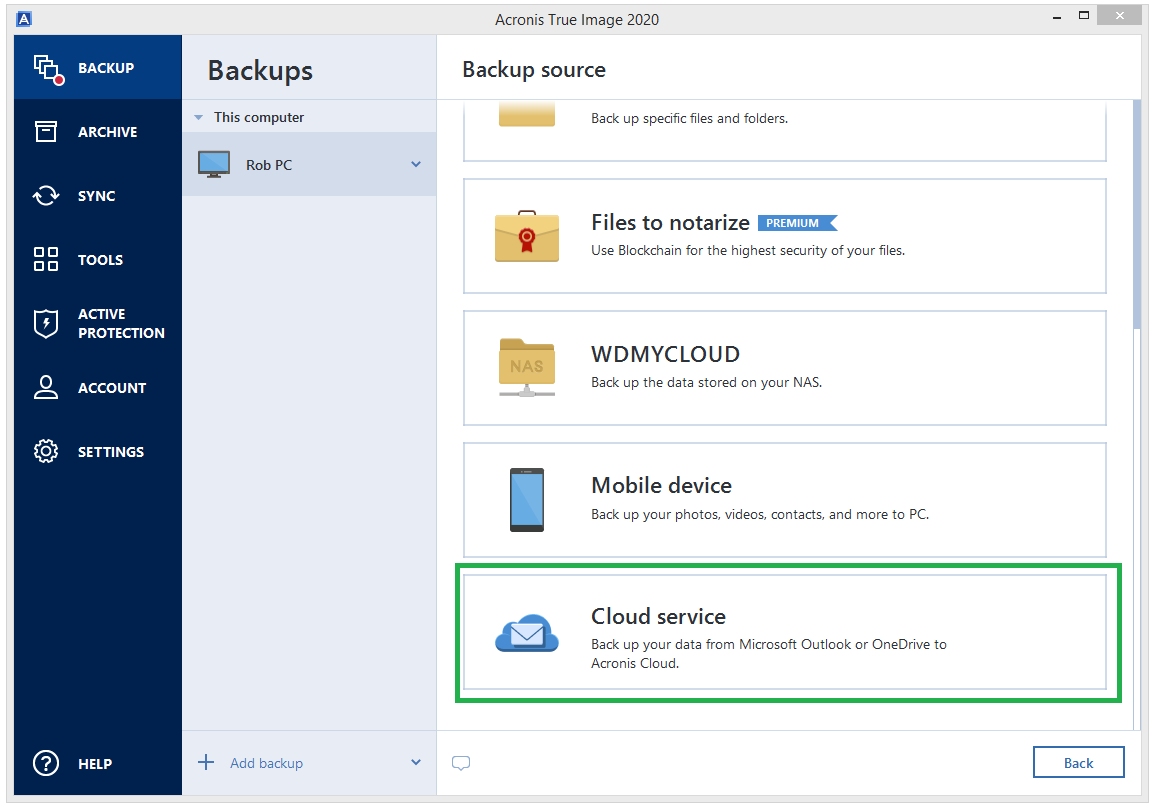
Office 365 Backup
Create direct cloud-to-cloud backups of your Office 365 account, including the emails and attachments from your Outlook.com mailbox and all of the files and folders in your OneDrive.
Active Disk Cloning
Make an exact replica of a Windows or Mac system while it’s in use, without having to stop and reboot. The easiest way to migrate your data – OS, files, applications, and settings – to a larger or faster disk.
Acronis Survival Kit
Create an all-in-one recovery tool on an external drive that contains everything you need to restart your system, including the required boot media and full image backups of your entire system.
Incremental and Differential Backups
Update backups up to three times faster with our Change-Block Tracker technology that follows modifications to an image in real time.
Non-Stop Backups
Keep working, playing or surfing: backups run in the background without affecting your computer’s performance. Continuously back up locally or to the cloud, capturing changes as often as every five minutes.
* Please note that all cloud-related features require a subscription to either the Advanced or Premium version of Acronis True Image 2020.
ENHANCEDEvent-Based BackupsPlug in an external USB and automatically begin backing up your data – it’s one of several event triggers you can choose to make protecting your data easier. Mac users can choose to back up in Power Nap mode.
Unlimited Mobile DevicesCover all of your family’s their smartphones and tablets with one license. Remotely managing the backup plan for each Android and iOS device using a single dashboard. Protect every photo, video, contact, and calendar appointment so they’re never lost – even if the device is lost or stolen.
Local Wireless BackupCreate backups of your mobile device automatically and wirelessly over Wi-Fi to your PC, Mac and NAS device. Back up by simply coming home.
Memory Card BackupProtect the data stored on your Android’s internal memory and SD storage cards to ensure nothing is lost.
NEW!Tray Notification CenterGet messages pushed to your desktop tray so you can monitor the status of your backups, quickly respond to any issues, and receive timely tips on how to enhance your protection.
Backup Cleanup UtilityFree up disk space by reviewing the backup files you have, manually selecting unnecessary versions, and deleting the files you no longer need. Gives you total control over your backup storage and versioning.
Visual Control of BackupsView the status of backups, file sizes, backup speeds, and number of backup versions. You’ll even see color-coded displays of how many photos, videos, music and documents are available to restore.
Flexible ManagementSchedule times, configure destinations, and select from full image, incremental, differential or custom backup types.
Version ControlKeep up to 99 versions of your backup if you want. Plus you decide how long you want to keep them – unlike other backup solutions, we let you choose how long they’re kept.
Try and DecideSafely test new software, drivers, system updates, and more knowing you can easily revert to your previous configuration.
Accessibility
Make data easily available from anywhere at any time
Anywhere Access
Retrieve any file or folder you need from your Acronis Cloud Storage backup from any computer or mobile device, and manage any backup plan on your account, all through our web-based console.
Cloud Restores
Enjoy the enhanced speed, reliability and stability of restoring from the cloud for a better overall performance, thanks to new backup technologies.
Data Center Choice
Select the data center nearest you to ensure the fastest connection and meet any regulatory requirements regarding where data is stored.
File Sync and Share
Sync files between computers or in the cloud so you can have the same files on multiple devices.
Universal RestoreEasily restore your system to the same or new hardware with our bootable media and driver injection technology. Your backed up data is quickly loaded on the machine of your choice.
Virtual Environment SupportConverting full image backups to a virtual hard disk format so you can run your system as a virtual machine. Mac users with Parallels Desktop 14 can recover backed up VMs as immediately bootable files.
ArchivingFree up disk space by moving large or rarely used files to the cloud or a local drive, while retaining easy access with a custom desktop shortcut.
WinPE Media BuilderCreate WinPE boot media so you can recover your system from backup when your computer does not boot. Our WinPE builder allows you to select the drivers that need to be added to the media for better hardware compatibility.
NEW!Custom Power ManagementKeep your laptop going by managing backups so they don’t drain the battery. You can set a minimum power level for backups, or completely block backups on battery power.
ENHANCEDMac RestoresRestore your data to a new Mac machine more easily, even if it is spread across APFS volumes on your current system.
Device FlexibilityAvoid being trapped in a single mobile platform by easily migrating data between Android and iOS devices.
Restore Individual FilesRetrieve just the file you need from your backup without recovering all of your mobile device’s content.
Mobile Backup ReviewBrowse the contents of your mobile backups directly on the local PC or Mac that stores the backup files.
Privacy
Control who has visibility and access to your data
End-to-End Encryption
Secure your backup using enterprise-grade AES-256 encryption that keeps your data private, whether it is on-site, in transit, or in the cloud. Not even Acronis can read your encrypted files.
User-Defined Passwords
Create encrypted backups for each individual family member that are protected by their own custom password.
Back Up on Selected Wi-Fi
Control how and where you back up to the cloud so you avoid the metered connections and unsecure public networks that can expose your data.
Hybrid Cloud
Store your backups in Acronis’ hybrid cloud infrastructure knowing that our data centers are specifically built for data privacy and security.
Authenticity
Create undeniable proof a copy is an exact replica of the original
Blockchain Notarization
Create a unique “fingerprint” for your data with Acronis Notary, which generates a blockchain-based certificate that gives you an easy and irrefutable way to confirm its authenticity*.
Electronic Signatures
Capture electronic signatures on documents from multiple people and record them in the blockchain ledger with Acronis ASign for an easy, efficient and secure way to verify an agreement’s integrity*.
* Please note that all blockchain-based features require a subscription to the Premium version of Acronis True Image 2020.
Security
Protect your data, apps, and systems against malicious threats
Integrated Anti-Ransomware
Prevent ransomware from encrypting your files, infecting your network, or crippling your system with Acronis Active Protection, our artificial intelligence and machine learning-based technology that detects and stops ransomware, and automatically reverses its effects. The latest version stops illicit service termination attacks and shows why an item was flagged.
Cryptomining Blocker
Detect and stop the kind of cryptomining malware that allows online crooks to infect personal computers to hijacking system resources to mine for cryptocurrencies and expose your machine to additional cyberthreats. Stop cryptojacking in real time and preserve your system integrity.
Secure Data Centers
Back up to our data centers knowing that each location is designed to meet the highest levels of security and include on-site protections such as armed guards, 24/7 video surveillance, biometric access, etc.
Security Dashboard
Monitor potential cyberthreats, identify blocked activity, and approve trusted applications so they run uninterrupted.
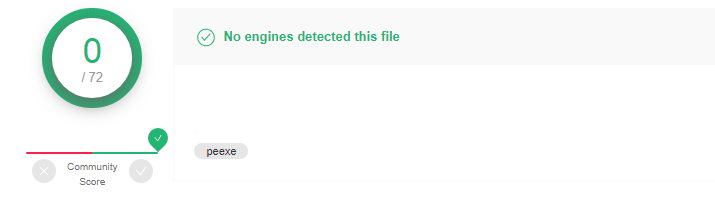
Virus Total Validation:
Download Links:
Download Acronis True Image 2020

Sorry, the comment form is closed at this time.